How to Optimize PGP Encryption for Better Results: The Definitive Guide
In an era where data breaches and digital surveillance are becoming increasingly common, protecting your sensitive information is no longer optional. PGP (Pretty Good Privacy) encryption remains one of the most robust methods for securing communications and files.
However, simply “using” PGP is not enough. To achieve better results in terms of both security and efficiency, you must know how to optimize the protocol. This guide provides a comprehensive roadmap for beginners to master PGP encryption and its underlying Public Key Infrastructure (PKI).
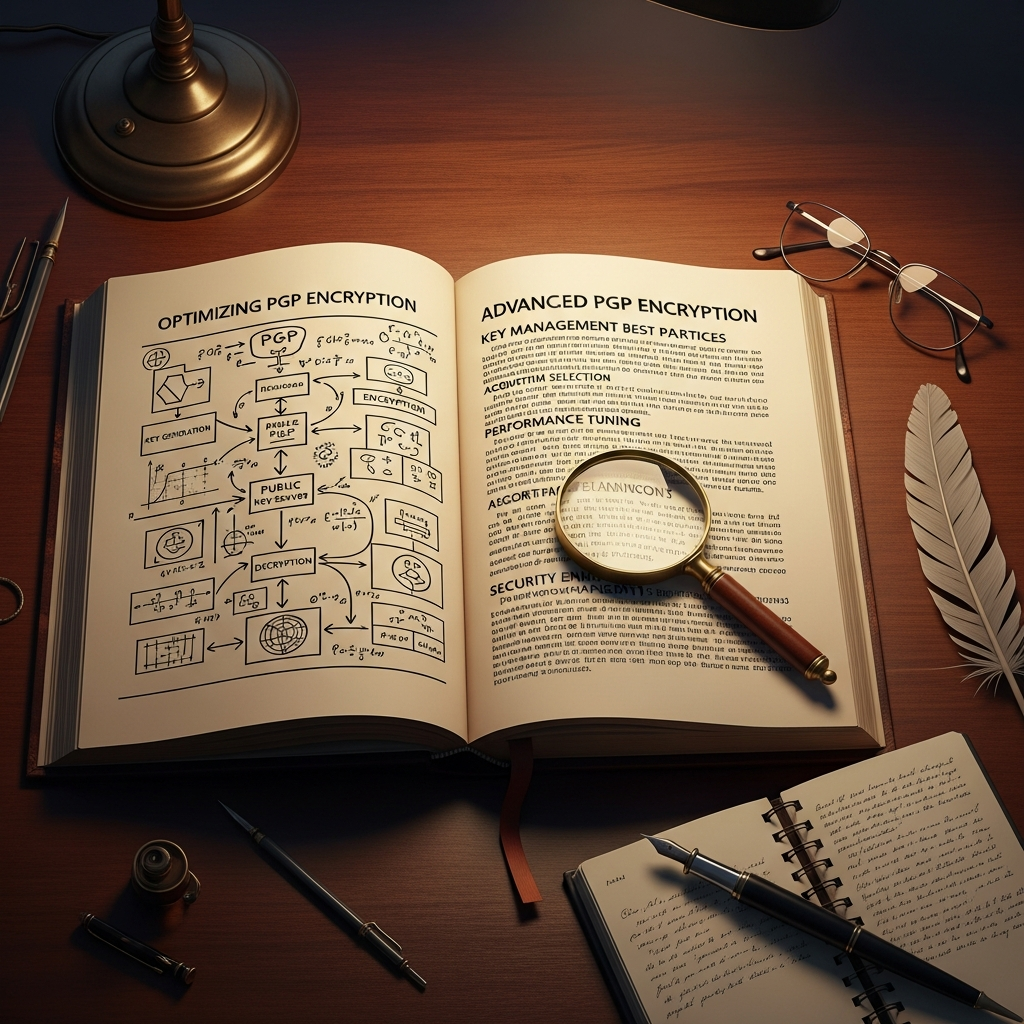
Understanding the Fundamentals of PGP Encryption
Before diving into optimization, you must understand what PGP is. PGP is a data encryption and decryption program that provides cryptographic privacy and authentication for data communication. It uses a hybrid cryptosystem, combining symmetric-key encryption and public-key encryption.
When you use PGP, you work with a “key pair”: a Public Key (which you share with others) and a Private Key (which you keep secret). This foundation is what makes data security possible in an untrusted environment.
Optimizing this process ensures that your encryption software runs smoothly, your keys remain uncompromised, and your digital signatures are verifiable by your recipients without technical hurdles.
Why Optimization Matters for Data Privacy
Many users fail to realize that outdated PGP configurations can leave them vulnerable. Optimization is not just about speed; it is about hardening your security posture. By following the steps below, you ensure that your privacy is maintained against modern computational threats.
- Enhanced Security: Using stronger algorithms prevents “brute-force” attacks.
- Improved Interoperability: Proper configuration ensures your keys work across different platforms.
- Future-Proofing: Preparing your setup for the eventual rise of quantum computing.
Step 1: Choosing the Right Algorithm for Maximum Security
The first step to optimize PGP is selecting the right mathematical algorithm. Not all encryption methods are created equal. For years, RSA was the industry standard, but the landscape is shifting.
RSA vs. ECC: Which Should You Choose?
Currently, you have two primary choices for key generation: RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography).
RSA is widely compatible but requires large key sizes (at least 3072 or 4096 bits) to remain secure. This can result in slower performance and larger file sizes. For better results in modern environments, many experts now recommend ECC.
ECC (specifically Ed25519) offers the same level of security as RSA but with much smaller key sizes. This leads to faster computation, lower power consumption on mobile devices, and more efficient key management.
Step 2: Advanced Key Management and Subkey Strategy
A common mistake among beginners is using a single “Master Key” for everything. To optimize PGP encryption, you should implement a subkey strategy. This separates your primary identity from your daily cryptographic tasks.
The Power of Subkeys
Your Master Key should only be used for two things: certifying other keys and creating subkeys. For daily tasks like encryption and digital signatures, you should generate specific subkeys.
By using subkeys, you can keep your Master Key in “cold storage” (offline). If your laptop is stolen, you only need to revoke the subkeys, not your entire identity. This is a crucial aspect of professional key management.
Pro Tip: Always set an expiration date for your subkeys (e.g., 1-2 years). This forces you to review your security setup periodically and mitigates the risk if a key is silently compromised.
Step 3: Hardening Your PGP Configuration File
If you are using GnuPG (GPG), the most popular open-source encryption software, you can optimize its behavior by editing the gpg.conf file. This file dictates how the software handles data.
To achieve better results, you should specify your preferred algorithms. Add the following lines to your configuration to ensure GPG defaults to the strongest settings:
- personal-cipher-preferences: AES256, AES192, AES
- personal-digest-preferences: SHA512, SHA384, SHA256
- cert-digest-algo: SHA512
- default-preference-list: SHA512, SHA384, SHA256, AES256, AES192, AES, ZLIB, BZIP2, ZIP, Uncompressed
These settings ensure that you are not accidentally using weak legacy protocols (like SHA1 or CAST5) when communicating with others.
Step 4: Implementing Digital Signatures for Authenticity
Encryption protects privacy, but digital signatures protect integrity and authenticity. A signature proves that the message has not been altered and that it truly came from you.
To optimize PGP results, you should sign every outgoing message, even if the content isn’t “secret.” This builds your reputation in the Web of Trust and allows recipients to verify your identity habitually. It prevents “man-in-the-middle” attacks where an attacker might try to impersonate you.
Step 5: Utilizing Hardware Security Modules (HSMs)
For those seeking the highest level of data security, storing your private keys on your computer’s hard drive is a risk. Malware can potentially scrape your keys from memory.
The solution is to use an HSM or a security token like a YubiKey. These devices are designed to hold your PGP subkeys in a way that they can never be exported. When you need to sign or decrypt, the computation happens on the device itself.
This optimization ensures that even if your computer is fully compromised, your private key remains safe. This is the gold standard for Public Key Infrastructure protection.
Step 6: Establishing a Revocation Strategy
Optimization is not just about the “happy path”; it is about planning for disaster. What happens if you lose your private key or your password is compromised? Without a revocation certificate, your public key will stay on keyservers forever, confusing your contacts.
Immediately after generating your Master Key, you must generate a revocation certificate. Store this certificate in a physical format (like a printed paper or an encrypted USB drive in a safe). This allows you to “kill” your key and notify the network that it should no longer be trusted.
Best Practices for Maintaining PGP Integrity
To keep your PGP encryption running at peak performance, follow these ongoing maintenance tips:
- Refresh Keys Regularly: Use the
--refresh-keyscommand to update your local keyring with the latest signatures and revocations from keyservers. - Verify Fingerprints Manually: Never trust a public key you downloaded from the internet without verifying its fingerprint via a secondary channel (like a phone call or a secure chat).
- Use Strong Passphrases: A key is only as strong as the passphrase protecting it. Use a long, random passphrase managed by a reputable password manager.
- Clean Your Keyring: Remove old, unused, or expired keys to prevent confusion and speed up software processing.
Common Pitfalls to Avoid
Even with optimization, certain habits can undermine your data security. Avoid these common mistakes:
- Storing Keys in the Cloud: Never upload your private key to services like Google Drive or Dropbox.
- Ignoring Metadata: PGP encrypts the body of an email, but not the subject line or the recipient’s address. Be mindful of what you write in the “Subject” field.
- Using Short Keys: RSA 1024-bit keys are now considered breakable by well-funded adversaries. Always aim for higher bit-depths or ECC.
The Future of PGP: Post-Quantum Considerations
As we look toward better results in the long term, we must consider Post-Quantum Cryptography (PQC). Traditional RSA and ECC algorithms are theoretically vulnerable to future quantum computers.
The OpenPGP community is currently working on integrating quantum-resistant algorithms. While not yet standard for everyday users, staying informed about these updates is part of a high-level optimization strategy for your digital signatures and long-term privacy.
Frequently Asked Questions (FAQ)
Is PGP still secure in 2024?
Yes, PGP remains extremely secure when configured correctly. Using strong algorithms like AES-256 and ECC ensures that your data is protected against current decryption technologies.
What is the difference between GPG and PGP?
PGP is the original proprietary software, while GnuPG (GPG) is the open-source implementation of the OpenPGP standard. Most people use GPG today because it is free and highly compatible.
Can I use PGP on my smartphone?
Yes, there are several mobile apps (like OpenKeychain for Android) that allow you to manage keys and perform PGP encryption on the go. However, ensure your mobile OS is secure and updated.
What happens if I lose my private key?
If you lose your private key and do not have a backup or a revocation certificate, you will be unable to decrypt any messages sent to that key, and you cannot officially tell others to stop using it.
Conclusion
Optimizing PGP encryption is a journey, not a one-time task. By selecting modern algorithms like ECC, implementing a subkey strategy, and using hardware security modules, you can achieve better results and ensure your data security is unassailable.
Remember, the goal of Public Key Infrastructure is to create a secure environment where privacy is the default, not the exception. Take the time today to audit your PGP setup—your future self will thank you for the extra layer of protection.